Integrated Windows Authentication
Integrated Windows Authentication (IWA) enables users to seamlessly authenticate using their Windows credentials. This method leverages protocols like NTLM (NT LAN Manager) or Kerberos to authenticate users without needing them to re-enter their credentials when accessing services or applications within the Windows domain.
MyQ X supports authentication via NTLM, utilizing a challenge-response mechanism. In this process, the user provides a hashed version of their password, and the server validates it without needing to know the actual password.
If your client computer belongs to the domain (for example, an intranet application), the user does not need to enter credentials.
Prerequisites
The following requirements must be met to utilize IWA:
Active Directory Domain Services (AD DS) should be installed and configured.
Devices and MyQ servers must be joined on the same local domain.
Proper DNS configuration is vital to ensure accurate domain name resolution.
Devices are running Windows.
Users must be synchronized from Active Directory and use it as their authentication server in MyQ.
To use silent IWA in the Desktop Client, “Sign in with Windows Authentication” must be enabled on the server in Settings – User Authentication.
Configuration
IWA is usually enabled by default and doesn't require extensive configuration unless specific security policies need to be enforced. Configuration is primarily managed via Group Policy and IIS (if you are running your applications; IIS is not required for authentication with MyQ), and it typically works automatically within a properly configured domain environment.
On clients, it must be ensured that Windows Authentication is enabled in web browsers and that MyQ server is added as an intranet website in the same tone as client computers.
Domain Controller
NTLM settings can be easily managed through Group Policy. To do this, open the Group Policy Management Console (GPMC) and go to
Computer Configuration -> Policies -> Windows Settings -> Security Settings -> Local Policies -> Security Options. Within this section, you will encounter various policies concerning NTLM, including Network security: LAN Manager authentication level.
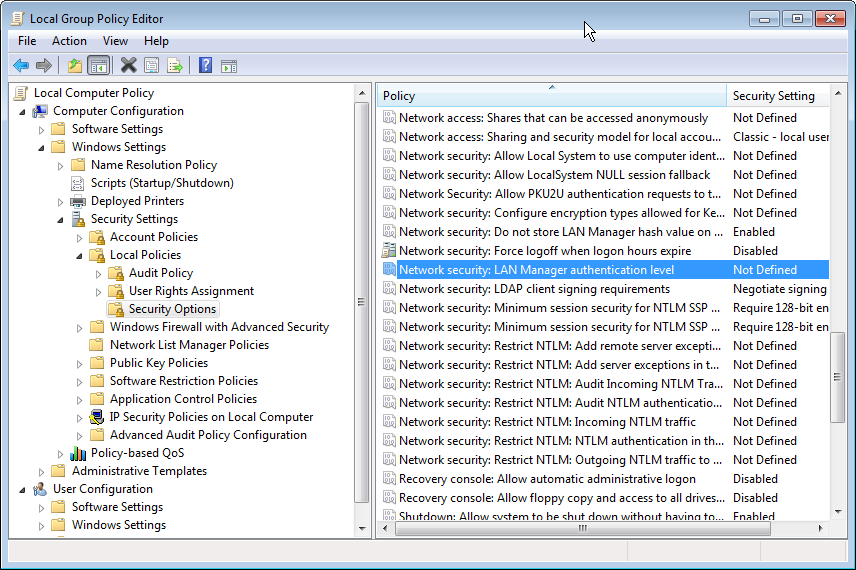
Please validate that these settings meet your security requirements. For instance, you have the option to set the LAN Manager authentication level to permit only NTLMv2 responses, which is a more secure choice compared to NTLMv1.
Client Configuration
Ensure that clients are configured to use Integrated Windows Authentication (IWA). This usually requires configuring web browsers (such as Edge, Chrome, or Firefox) to enable automatic logon using the current username and password for intranet sites.
Microsoft Edge
Internet Options → Advanced → Security → Enable Integrated Windows Authentication.
Internet Options -> Security -> Local intranet -> Sites -> Advanced, add the intranet sites here. Then go to Custom level -> User Authentication -> Logon -> Automatic logon only in Intranet zone.
User Login Experience
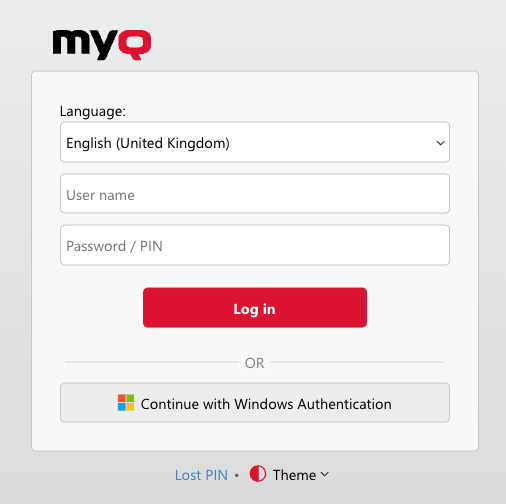
Windows Authentication on the MyQ Web Interface
Windows Authentication can be enabled in Settings → User Authentication. Once this is done, a new login method is displayed on the login screen. This ensures that users can still use other forms of authentication if IWA does not apply to them (for example, guest users, BYOD users, *admin account).
If Windows Authentication fails for the user, they are redirected back to the standard login experience and can continue with another login method. The error message Invalid credentials will be displayed.
Windows Authentication in MyQ Desktop Client
Windows Authentication can be enabled in Settings → MyQ Desktop Client for specific configuration profiles. This way, you can enable this option only for certain computers while selecting standard login with MyQ credentials or credentials validated via LDAP against a remote user directory (e.g., AD) on another set of computers.
If Windows Authentication fails for the user, they are redirected back to the standard login experience and can input MyQ credentials or log in with credentials validated via LDAP against a remote user directory (e.g., AD).
.png)